Confidential Coordination IV: What the Interfold Makes Possible
This essay is the fourth and final in a series on confidential coordination. It shows how fairer markets, stronger collective decisions, and collaborative intelligence become possible without exposing private inputs or concentrating execution.
Digital systems no longer just move information around. They determine outcomes: who wins, what clears, what gets counted, what can be known together.
More and more, those outcomes are produced in multiparty settings. Markets aggregate bids, liquidity, and allocation across participants. Institutions coordinate sensitive datasets across organizations. Governance systems turn private preferences into collective decisions. Model-driven systems and agent networks will extend this pattern further across people, organizations, markets, and protocols.
As systems become more multiparty, coordination does not become less important. It moves closer to the center of economic and political reality.
But when shared outcomes depend on private inputs from multiple parties, the same problem keeps returning: the process still has to be run somewhere. In these systems, someone may have privileged visibility, govern execution, or control release at the moment the outcome becomes real.
The Interfold changes that structure. It allows private inputs to produce shared, verifiable outcomes under distributed enforcement, rather than passing execution through one operator, one enclave, or one custodial pipeline. The result is not just more private computation. It is a different way of structuring how outcomes are formed.
The first three essays in this series defined confidential coordination, argued that it requires a network, and showed how execution becomes distributed across that network. This final essay turns to what follows: what becomes possible when shared outcomes no longer have to pass through a single point of control?
Three coordination types
Confidential coordination matters most when private inputs have to become outcomes that others can rely on. A bid becomes a price. A vote becomes a tally. A dataset contributes to a metric, model, risk score, or shared signal.
The difficulty is not simply keeping those inputs private. It is producing a result that can be verified without exposing the inputs or giving one party control over the process that forms it.
That pattern appears most clearly in three recurring forms: competitive coordination, collective coordination, and data coordination. In each, the Interfold changes how the outcome is produced, verified, and released.
Competitive coordination: Toward fairer market mechanisms
Competitive coordination covers situations where private inputs determine a winner, a price, or an allocation. This already appears across procurement, sealed-bid markets, allocation processes, and DeFi, where auctions and auction-like mechanisms are used to clear assets, allocate blockspace, match liquidity, or determine prices. In these settings, the field itself should remain hidden until the result is finalized.
- Current constraint: Competitive processes often still give some operator, sequencer, auctioneer, or execution environment visibility into how the field is taking shape. In practice, that can mean access not only to bids, but to failed bids, edge conditions, partial signals, timing information, or other traces of strategy that become structural advantage.
- What changes with the Interfold: A winner, price, or allocation can still be produced and verified, but the positions that generate it do not need to be visible during execution. Only the permitted result is released.
What this unlocks: This makes room for fairer market mechanisms: systems where operators and privileged observers have less structural advantage, and where participation does not depend on making visibility part of the game.
Collective coordination: Toward more legitimate decisions
Collective coordination covers situations where private preferences or choices have to become a legitimate shared decision. This appears in secret ballots, governance voting, committee selection, ranking processes, and other settings where participation must remain confidential even as the result becomes binding.
- Current constraint: Collective processes usually have to reconcile secrecy, counting, and final release through a trusted counter: an institution, an operator, an administrator, or another centralized authority. Legitimacy still tends to depend on a point of concentration at the moment the outcome becomes real.
- What changes with the Interfold: A tally, selection, or governance outcome can still be produced and verified, but private participation no longer has to collapse back into centralized counting.
- What this unlocks: This strengthens the conditions for collective decision-making: participants can keep their choices private without making legitimacy depend on a trusted tallying authority, reducing exposure to coercion or pressure.
Data coordination: Toward collaborative intelligence
Data coordination covers situations where multiple parties contribute data or signals in order to derive a shared result. This appears in cross-institutional analysis, confidential model evaluation, joint medical or financial research, collaborative analytics, and emerging AI workflows. In these cases, the value lies in the model, metric, risk score, or shared signal, not in centralizing the underlying data.
- Current constraint: Shared computation across sensitive datasets usually begins by reducing the collaboration to what can be safely disclosed, pooling the data with a custodian, or narrowing the question until the risk becomes manageable. The output may be valuable, but authority still accumulates around whoever controls the process that produces it.
- What changes with the Interfold: A metric, model evaluation, aggregated analysis, or shared signal can be produced without surrendering raw inputs into one operator’s environment. Shared computation no longer has to begin from pooled custody.
- What this unlocks: This creates stronger conditions for cross-institutional collaboration. Shared intelligence can be produced across boundaries without turning one participant into the custodian of everyone else’s data.
One execution pattern across all three
These coordination types differ in context, but not in shape. Competitive systems produce winners, prices, or allocations. Collective systems produce tallies, selections, or governance outcomes. Data systems produce metrics, model evaluations, risk scores, or shared signals.
In each case, multiple independent parties contribute private inputs to produce one shared outcome. The domain changes. The execution pattern does not:
In the Interfold, the path from private input to shared outcome is implemented through distributed execution:
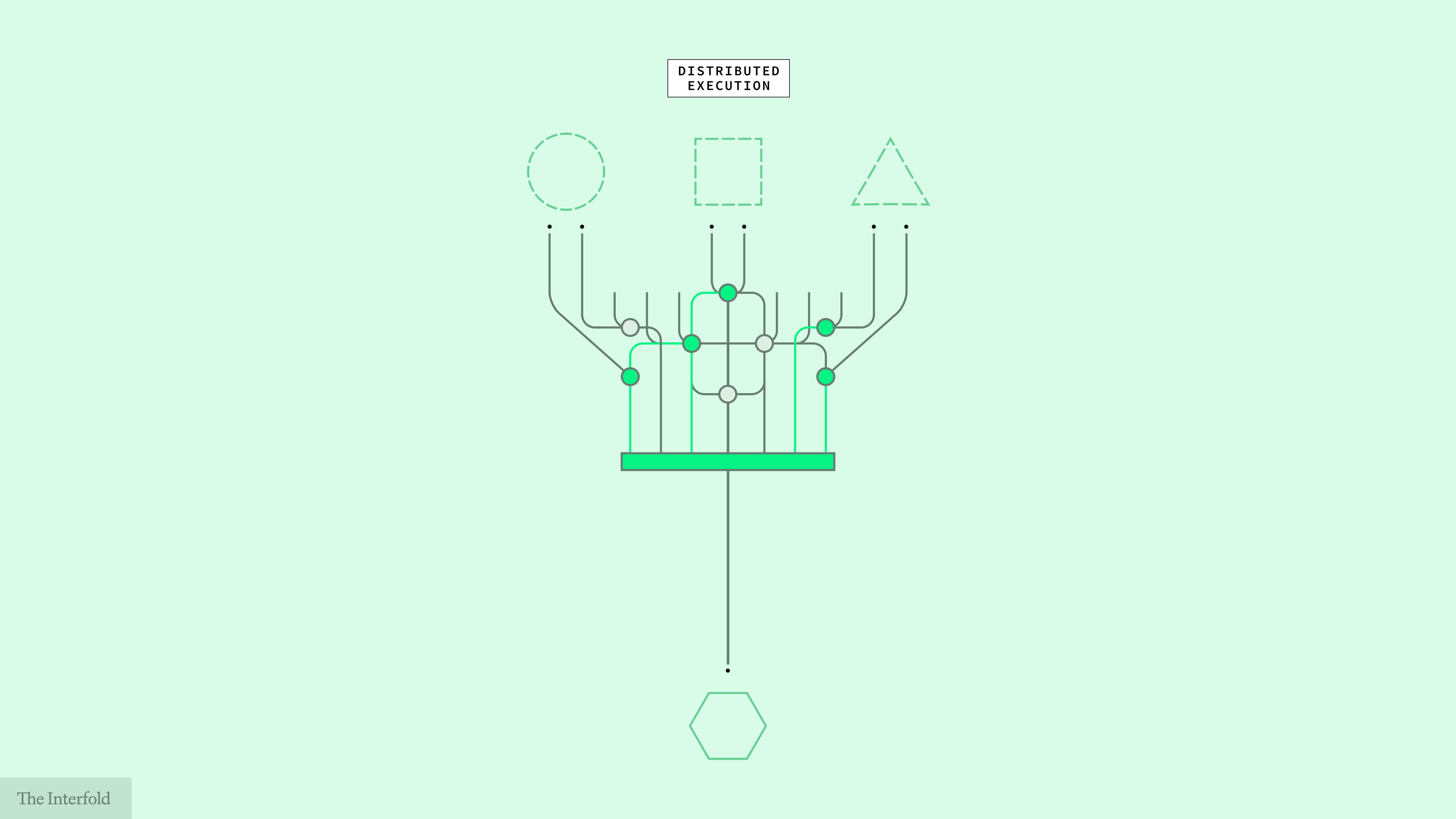
Inputs are first submitted in encrypted form. A program defines how they will be processed within an Encrypted Execution Environment instantiated for that computation. Execution is enforced by ciphernodes across the network rather than inside an environment controlled by one operator. The result can be verified as valid, and release is governed by threshold conditions rather than one party’s discretion.
What stays private are the underlying inputs and intermediate state. What becomes shared is the outcome others need to rely on.
What changes when execution no longer concentrates control
The consequence is the same across all three coordination types: the outcome can become shared without making the underlying positions, preferences, or datasets available to whoever runs the process.
That changes more than confidentiality. Market mechanisms can be structured around fairness of process rather than privileged visibility. Collective systems can produce authoritative outcomes without concentrating trust in one counter. Shared computation can become a basis for collaboration without first requiring centralized custody.
What becomes possible is not simply a privacy layer on top of familiar systems. It is a broader class of systems in which visibility, custody, and control no longer have to converge at the moment outcomes are formed.
A new execution model
None of this makes coordination easy. Incentives still diverge. Adversarial conditions still exist. Institutions still need rules, governance, and legitimacy beyond the computation itself. Confidential coordination does not erase those realities.
It changes one of the background assumptions that has shaped digital systems for decades: that producing shared outcomes requires concentrating execution somewhere.
That assumption has consequences. When execution concentrates, power concentrates with it. Markets become easier to manipulate by whoever sees the field first. Collective decisions depend on institutions trusted to count and release results. Shared analysis requires someone to hold the data, narrow the question, or absorb the liability. The structure of execution becomes the structure of permission.
The Interfold is built for that layer. It does not solve politics, replace institutions, or make incentives disappear. It changes something more specific: whether producing an outcome requires making execution itself a point of concentrated authority.
Confidential coordination is not a feature added to existing systems. It is a different execution model: one in which shared outcomes can be formed without making privileged visibility, centralized custody, or unilateral release the price of participation.
As digital systems become more multiparty and more automated, coordination becomes more critical, not less. The question is not just who controls data. It is who controls the process by which private inputs become shared reality.
For decades, digital systems scaled by concentrating execution. The Interfold enables something different: systems that can produce shared outcomes at scale without concentrating the power to form them.

Participate in the Interfold network
A distributed network for confidential coordination.
Run a Genesis Ciphernode: Help operate the network by executing computations without exposing underlying data.
Build on Interfold: Create applications that coordinate across private inputs and produce verifiable outcomes.
Follow the Interfold: Track the network as it evolves, with updates, early use cases, and the emergence of a distributed system in practice.